Phishing Emails
What are phishing emails?
Phishing emails are illegitimate emails sent to recipients for the purpose of gaining sensitive information. These emails come in a few different types.
Phishing
Phishing emails are sent in bulk from one sender to many recipients. The sender hopes that a portion of the recipients will be susceptible to the email and will give up personal or financial information.
Spear Phishing
Spear phishing is a type of phishing that uses real information to create an email that is tailored to one or a few recipients, to appear more legitimate. A phisher might be able to locate information on social media or other websites, and create an email that seems real.
Sextortion Emails
Sextortion emails are a hoax extortion scam. In this case, the sender claims to have installed malware on a recipient's computer, and recorded evidence of them engaging in sexual acts or viewing pornography. The sender threatens to release the compromising information to the recipient's contacts unless they are paid a ransom in bitcoin.
How do I identify phishing emails?
There are a number of red flags to look for when determining if an email is legitimate or not.
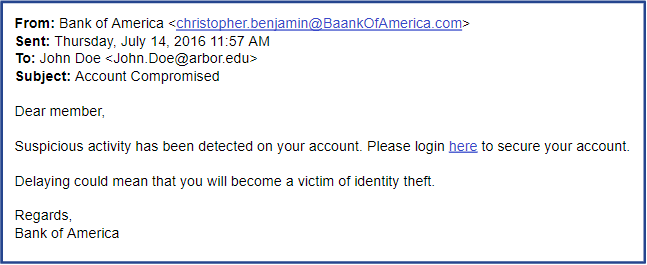
Impersonation
Jane Doe, CEO <[email protected]>
Human Resources <[email protected]>
Phishers will try to impersonate people or organizations that may seem familiar. Beware emails where the sender's name does not match the sender's email address.
Spelling/Grammatical Errors
Our staffs have found suspicious info on you account!.
Many phishing emails come from foreign actors that may not be fluent in English. Any email that contains misspelled words, grammatical errors, or added/missing punctuation is suspicious.
Inspiring an Emotional Response
Fraud detected! Login now to secure your bank account.
Phishing emails will often play on a sense of fear or urgency, trying to inspire a recipient to act quickly or irrationally without taking time to identify indicators of phishing.
Asking for Personal information
Please verify your identity here.
Phishing emails attempt to gain real information or login credentials from recipients. Most organizations will never ask for this information via email.
Contains Links
Phishing emails might contain links to unsafe websites. When you enter your credentials on these sites, phishers will steal the information and gain access to your accounts. Links can also be easily disguised. Read more about that here!
Phishing examples
Can you spot the red flags in these example emails?